Networking models are needed, especially if you want to learn DevOps. However, the fundamentals of networking are always skipped for the reason that they are going straight towards DevOps tools like Docker and Jenkins. We don't need to dive fully into networking, but a network is required for testing purposes. We must understand how these protocols work, as well as how to secure your deployed software, anticipate security flaws in code, and configure your infrastructure network. Knowing about the network models is a good foundation to start with.
Back in the old days, companies like IBM and Apple had their own networking models, which hindered them from communicating with each other because they had different models too. Networking models like OSI and TCP/IP were created so that different computers could communicate together, even with different devices. That's why you can communicate with Apple users even if you are using Windows.
There are many things to learn about the TCP/IP model. But, in this blog, I will dive into the basics only. So, you can grasp the idea of what TCP/IP actually is.
What is TCP/IP Model?
The TCP/IP Model saves the day by allowing you to communicate with people who use different models. TCP/IP stands for Transmission Control Protocol/ Internet Protocol, which are protocols or guidelines on how computers should be connected to the internet in order to communicate with other computers and, importantly, how to share data between them over the internet.
TCP and IP has different role to each other in the data transmission process. IP obtains the address, what we call an IP address, where data is sent. While the TCP is in charge of delivering data, after that IP address has been discovered, it makes sure that it is delivered accurately. To put it in a scenario, IP sorts the mail and TCP sends and receives the mail. Nevertheless, they are frequently used together, thus there is no need in separating them.
Difference between OSI Model and TCP/IP Model
Between OSI and TCP/IP, TCP/IP is the one being implemented in our computer system. However, OSI model are mostly and widely referenced known but TCP/IP are being used in practice. That's why it is also important to learn about TCP/IP because it the one being used even though they are not much different between them. TCP/IP model is the shorten version of OSI model.
Five Layers of TCP/IP Model
There are numerous functions, protocols, and algorithms that go into creating a computer communication system. These can be found on layers. When a user sends data via these layers, the TCP/IP model does so in a specific sequence, and then does so again in the opposite order when the data is received. We divide those functions into layers to make things simpler. When a computer connects, each of these layers defines the protocols.
These are the five layers of TCP/IP model:
- Layer 1: Physical Layer
- Layer 2: Data-Link Layer
- Layer 3: Network Layer
- Layer 4: Transport Layer
- Layer 5: Application Layer
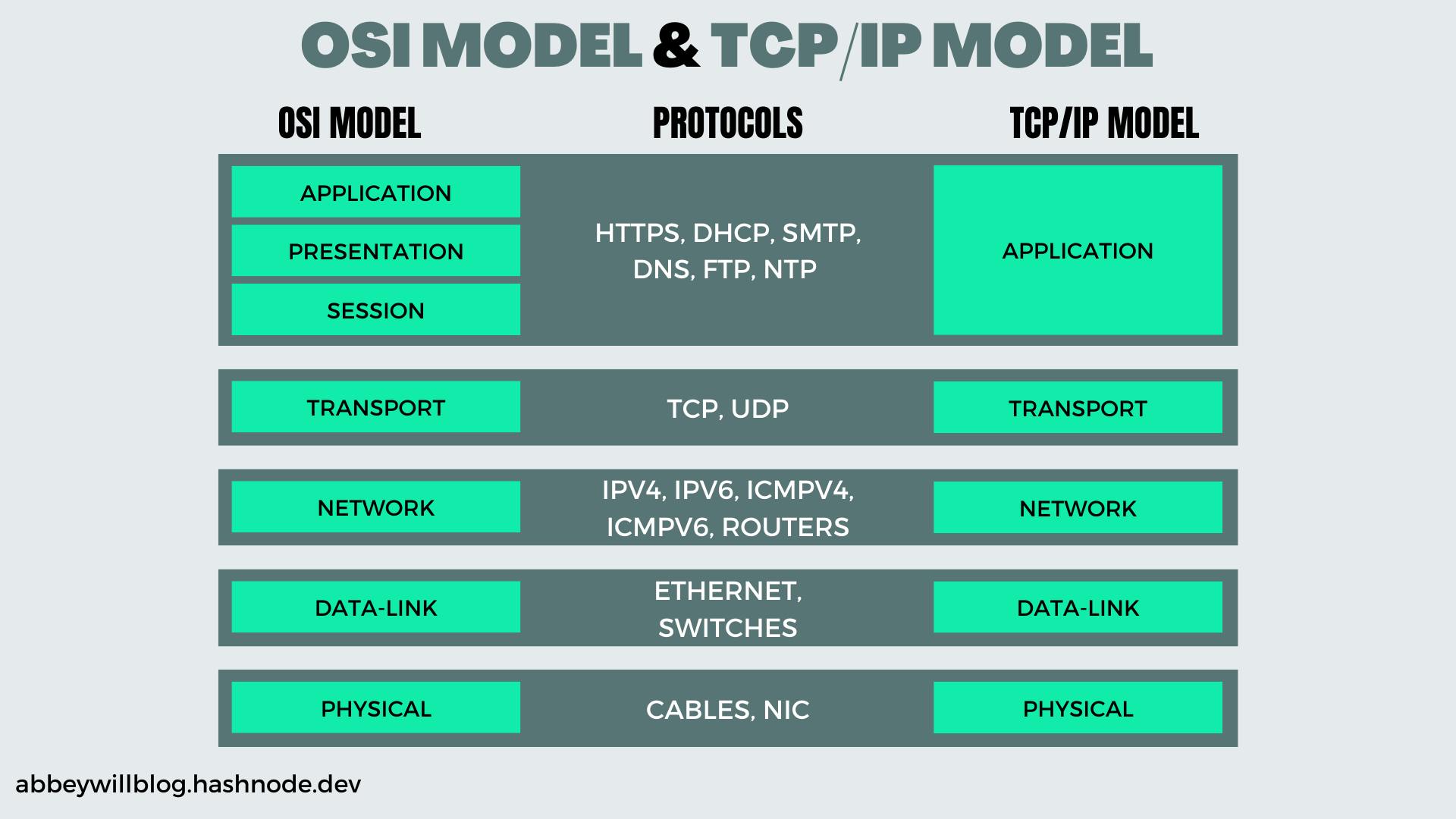
In the diagram, you can see that this is the new model of the TCP/IP model in which there are already five layers. The link layer has been split into physical and data-link layers. The direction of the model depends on whether you are sending or receiving traffic.
Layer 1: Physical Layer

The physical layer that enables computer communication across the internet. Basically, the physical layer is how the data should be sent physically through the network, which transfers bits over individual links. Ethernet cables, network interface cards, computer device drivers, and so on are examples of this.
Actual communication takes place at the physical layer. We are aware that communications are represented digitally by a series of 0s and 1s. This binary sequence is transformed into signals by the physical layer and sent across local media.
Layer 2: Data-Link Layer

The data-link layer is used to transmit data through the use of Ethernet frames. It deals with data translation from the upper layers to the physical layer and information transmission between hosts on the same local network. On the sender side, data-link is in charge of bit-by-bit transforming data streams into signals and transmitting those signals via the underlying hardware. On the receiver side, the data link layer receives data from hardware that is in the form of electrical impulses, puts the data together into a recognizable frame format, and then passes the frame format to the upper layer. In order for network devices to communicate, it is in charge of defining a standard method of interpreting the signals from the physical layer.
The data-link layer has two sublayers:
- Logical Link Control (LLC Sublayer) - It deals with flow control and error control
- Medium Access Control (MAC Sublayer) - It deals with data encapsulation and accessing the media
Layer 3: Network Layer
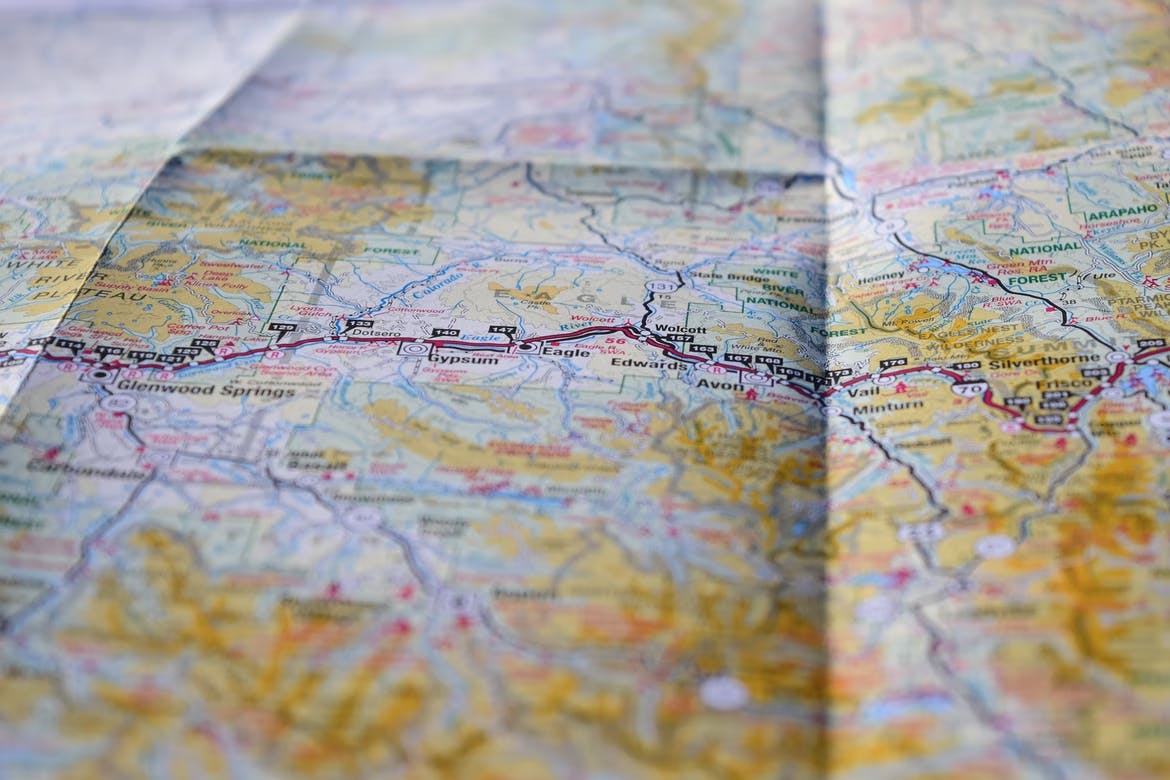
The Network Layer is in charge of distributing data over a group of networks. It describes how data is sent and received over the internet. The process includes addressing, transmitting and receiving packets. The source and host addresses, or IP addresses, are also part of the network layer. The network layer adds IP addresses to the TCP diagram to form IP packets and then uses routers to send these packets to the other networks. Through routers, it enables communication between various networks. Routers select the optimum route to the destination network and control traffic flow and routing to ensure data is transferred promptly and accurately. The network layer is also in charge of mapping various addressing schemes and protocols from source to destination.
Layer 4: Transport Layer

A secure connection is established between two communicating devices by the transport layer. TCP describes retransmitting missed packets, conveying data in the same sequence as it was sent, and controlling factors affecting data transmission pace. On the sending side, the transport layer splits up the application-layer messages it receives from a sending application process. When a datagram is received, the network layer separates the transport-layer segment from it and sends it up to the transport layer. Additionally, it enables synchronous end-to-end communication between apps.
Basically, the transport layer divides large data chunks into smaller chunks, known as segments, that can be transferred over the network more simply and are less likely to cause transmission issues should an error occur. The transport layer serves the application layer by providing ports, each of which each represent a separate application.
Layer 5: Application Layer

The host apps' and protocols' interaction process is outlined in the application layer. For the purpose of utilizing the network, the applications engage in this interaction with the transport layer services. Additionally, it defines the protocols that TCP/IP applications will employ.
Applications offer an interface that users can access through HTTP, much like a web browser. When delivering or receiving data, the end user uses and interacts with this. The main purpose of the application layer is to make it possible for users to access the Internet through a variety of applications. The application layer outputs data from the network in a protocol-compliant format.
Example scenario of the OSI model
Now, as you've seen the pictures per layer, imagine you're ordering a meal. The physical layer is the vehicle that will be used to deliver your food. The data link is how the vehicle will go from one intersection to the next. The network layer identifies which road is best to take to get into your house faster. The transport layer is when it will notify you that the food has arrived at your house. The application layer is your food.
Wrap-up
Now, how to remember all the names of the layers? Remember the layers this way:
- Please | Physical
- Do | Data-Link
- Not | Network
- Throw | Transport
- Avocados | Application